[vc_row][vc_column][vc_column_text]Each day more and more apps are created to make our lives easier. Some of these apps use technologies created decades ago but with new formats, new applicability and new interfaces to meet the demand of current users. One example of these technologies is the RFID (Radio Frequency Identification) that uses radio frequency to detect and capture data.
This technology was first used in the World War II, as a tracker for aircrafts in the territories of the countries involved in the conflict. Since then the technology usability has been more focused on pacific matters, such as retail. Using radio frequency tags, it is possible to detect information about price and availability of a product, for example. RFID presents itself as a great option to substitute vulnerable barcode systems, once problems with worn out tags and cloned tags will be eliminated.
RFID system is basically formed by few items, which seems very attractive when considering resources. To get a RFID system started you will need an antenna, which will work as a long-range radar, a decoder, which will read the code and transfer the information to a device, and a radio frequency tag, that will hold information like price, model and name of the product. Once detected by the antenna, the information stored in the tags will be read by radio frequency waves and translated to a digital environment. The information will be sent to computers or mobile devices, enabling a faster speed communication, transferring, collecting and using information.
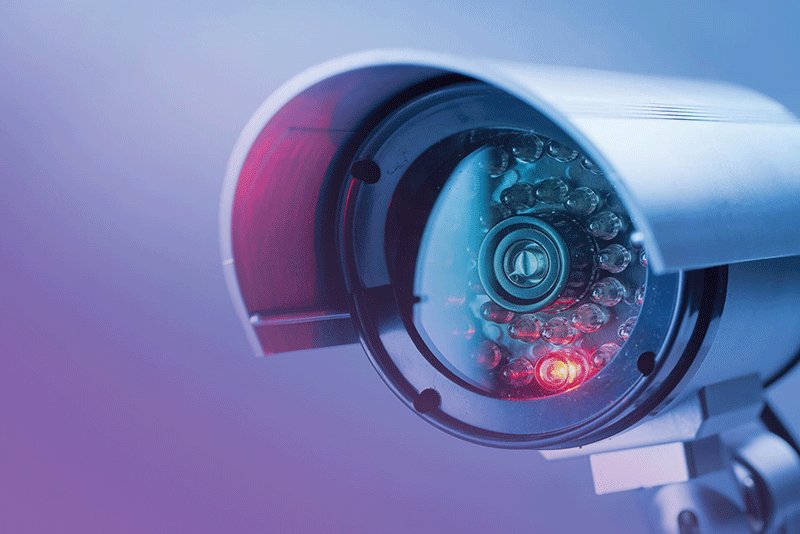
[/vc_column_text][vc_row_inner][vc_column_inner width=”1/2″][vc_column_text]Even though RFID systems have many qualities, information safety is still an issue. Anybody can have direct access to the tags and it can cause serious problems. Besides that, even short-range tags can be intercepted, opening way for malicious access. Exposing personal or even companies’ information, making the use of the technology a very dangerous option.[/vc_column_text][/vc_column_inner][vc_column_inner width=”1/2″][vc_video link=”https://youtu.be/8hnYz9szpDM”][/vc_column_inner][/vc_row_inner][vc_column_text]Another problem related to the use of RFID technology is that, just like barcodes, the tags are vulnerable in many situations. In access control for example, there are many cases of cloned, photographed and duplicated tags, limiting the safety provided by this technology.
A little parsimony can be used to choose the best technology, besides the variety of applicability and popularity of smartphones. Especially concerned about access control and payments. It is very important to be aware of vulnerability and data sharing privacy.[/vc_column_text][/vc_column][/vc_row][vc_row css=”.vc_custom_1528243334841{margin-top: 0px !important;border-top-width: 0px !important;padding-top: 0px !important;}”][vc_column][ultimate_icons][/ultimate_icons][/vc_column][/vc_row]